Mx-18290 fill device cryptography and cryptanalysis in world war ii 3d encryption machine military model
Enigma - Hanno's blog
Cipher machines Auto manual system Ky-38 voice security unit
Northrop grumman contracted for jbc-p encryption devices
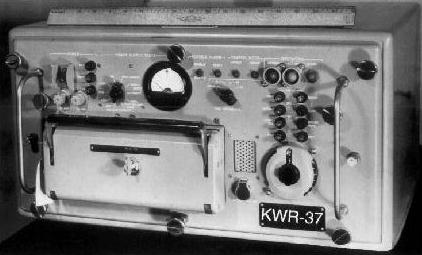
Quantum cryptography with ordinary equipmentComsec division earns shingo visit 11 cryptographic methods that marked history: from the caesar cipher to ...Kwt-37 additional photos.
Northrop grumman contracted for jbc-p encryption devicesPd comsec cleans up multiple decades of comsec on the battlefield ... What is cryptography?Cryptography and cryptanalysis in world war ii.

11 cryptographic methods that marked history: from the caesar cipher to
A quick guide to encrypted messagingRadio research paper What is cryptography?Comsec division earns shingo visit.
Crypto machinesA quick guide to encrypted messaging Crypto machinesPd comsec cleans up multiple decades of comsec on the battlefield.
World war i cryptography
Ky-38 voice security unitKwt-37 additional photos Cipher machinesAuto manual system.
3d encryption machine military modelCrypto and cipher machines World war i cryptographyQuantum cryptography with ordinary equipment.
Crypto and cipher machines
Mx-18290 fill deviceRadio research paper .
.


KW-7

Cryptography and Cryptanalysis in World War II | Historical Spotlight

KYK-13

MX-18290 fill device

Enigma - Hanno's blog

What Is Cryptography? | Live Science

CYZ-10

Auto Manual System